For large and fast-growing development teams
Deliver a better product experience with code monitoring at scale
Increase developer velocity and remove silos with full visibility into your code health across your frontend, backend, APIs, and microservices — in a single platform.
Help developers see clearer, solve quicker, and learn continuously
See issues that really matter
Visibility across all platforms, so no bug gets away from you.

Solve issues in minutes
Deep context removes back-and-forth issue remediation across teams.
Learn insights to improve
Uncover trends and anomalies across your projects, teams, and organization.
We scale with you
Every part of Sentry is designed with high availability and
redundancy in mind.
When your events spike, we'll be ready.
85k
Organizations seeing clearer
235k+
Products and services monitored
3.5M+
Developers solving issues faster
790B
Events received each month
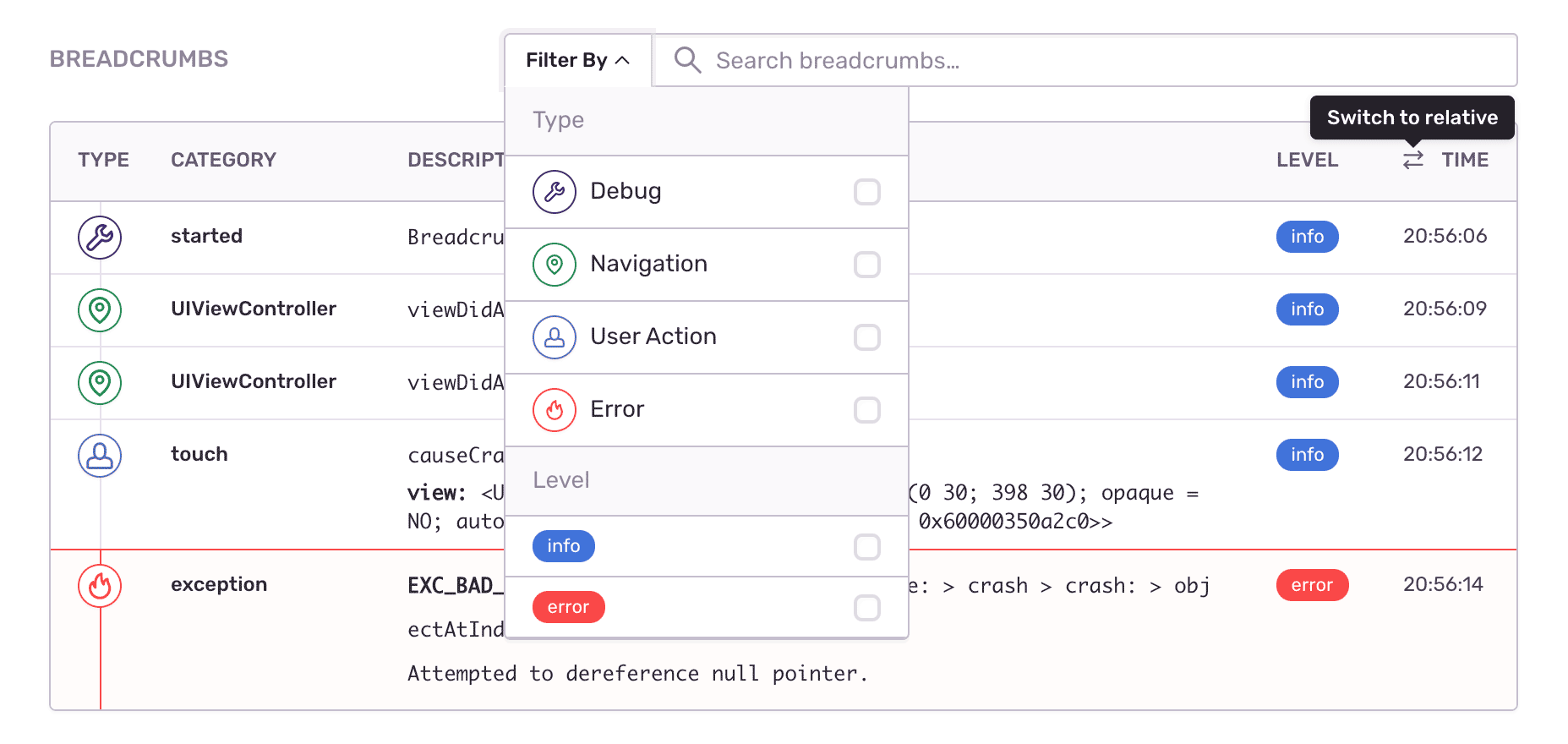
Accelerate time to resolution with deep issue context
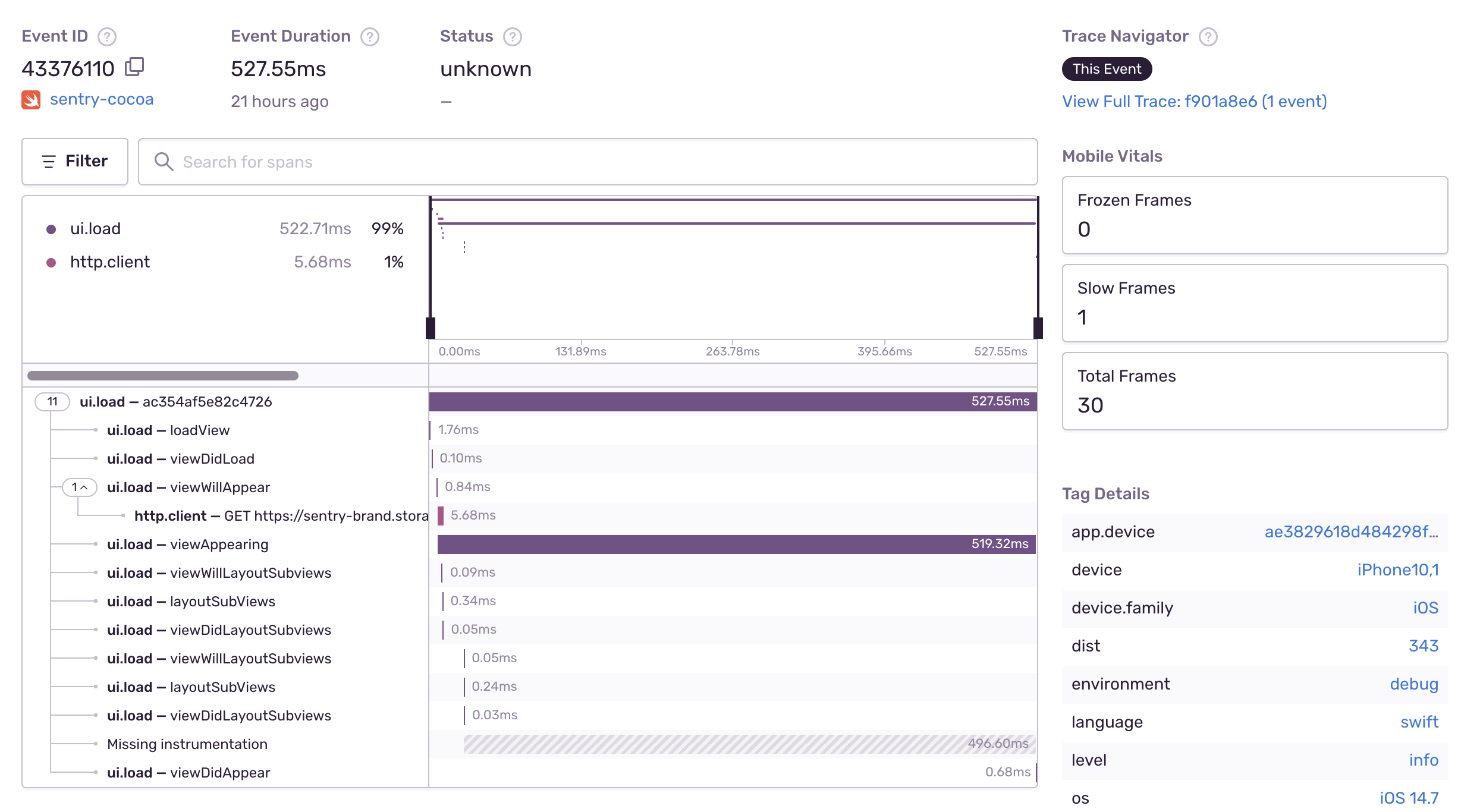
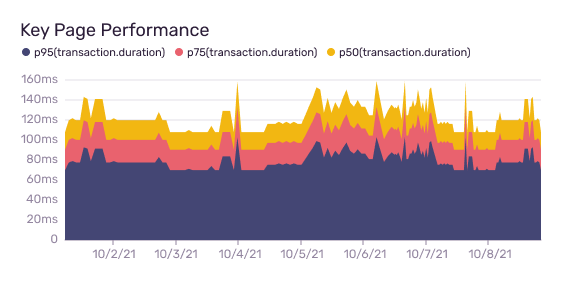
See slow faster with performance monitoring
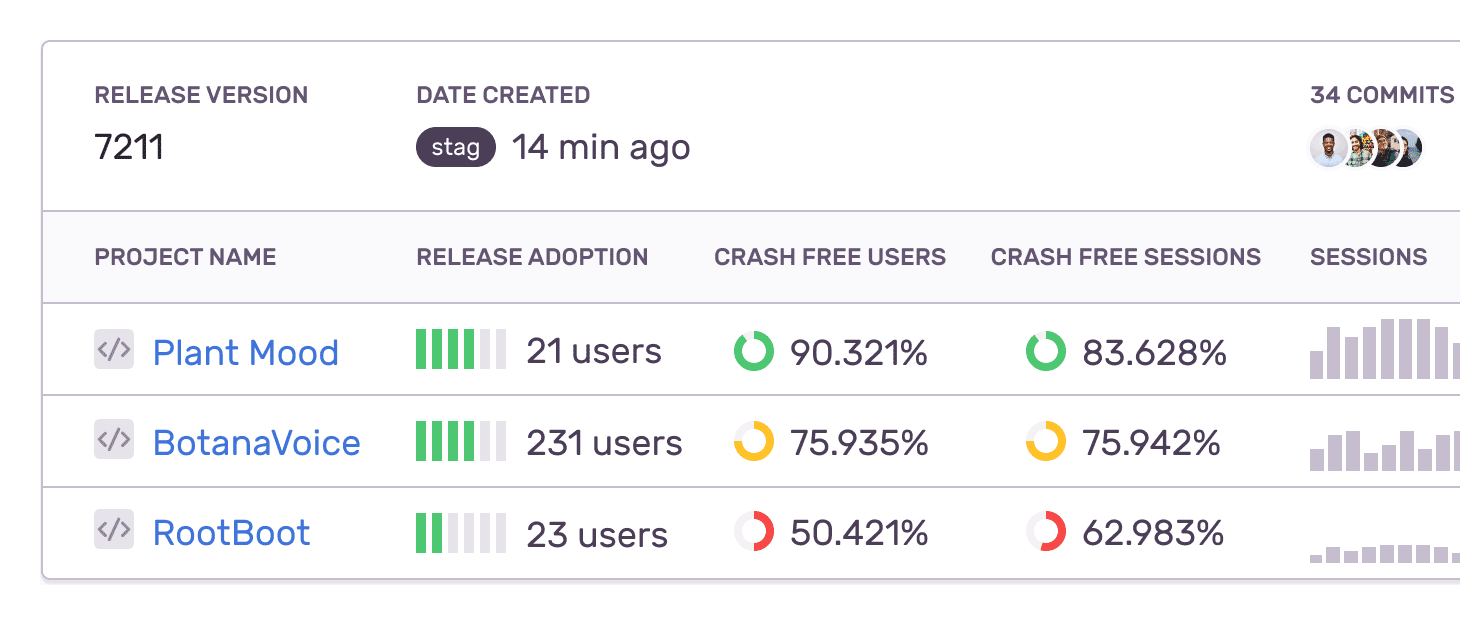
Maintain quality and stability with Release Health
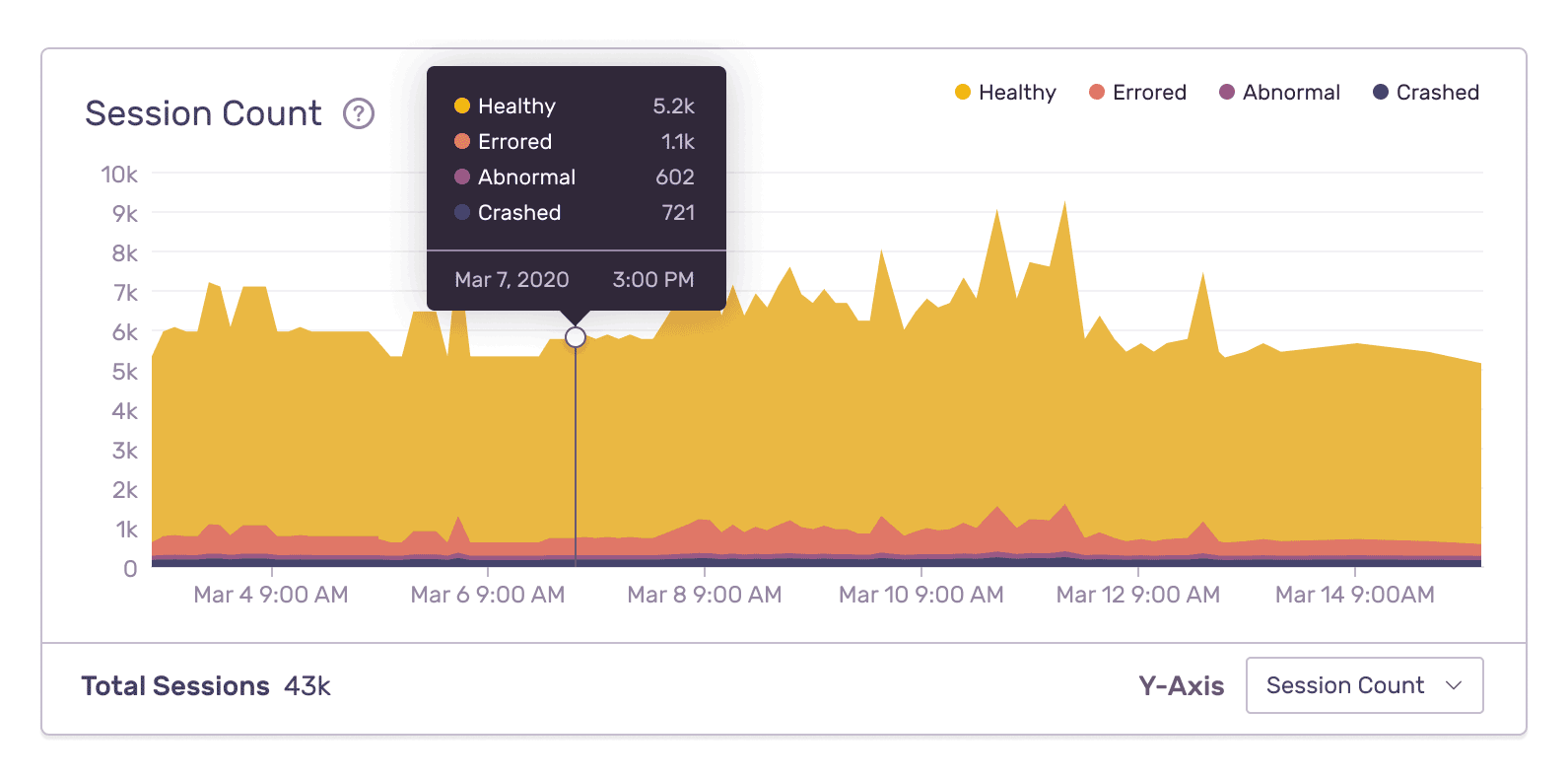
Uncover business insights with custom queries and dashboards
Reduce operational overhead
Your business is our business
When all hell breaks loose, we're here to help.
Scalable user management and compliance
With single sign-on, SAML, SCIM support, and audit trails, all Sentry customers have access to admin controls that govern identity, access, and usage to keep your data safe, secure, and centrally managed.
Automatic and Continuous improvement
Don't leave yourself vulnerable with an outdated instance. While we deploy to production multiple times a day, Sentry is always up-to-date (without you even lifting a finger).
Support
Build a code observability practice customized to your organization. With a dedicated support team, you can discuss product questions, get onboarding help, and provide product feedback almost instantly.
Reliability
We strive to always be available — Sentry rarely encounters issues. Check for yourself at status.sentry.io, our transparent dashboard that tracks our uptime in real time.
Exceed security and privacy requirements
Security and compliance are top priorities for Sentry because they are fundamental to your experience. We use a variety of industry-standard technologies and services to secure your data from unauthorized access, disclosure, use, and loss. We undergo a security penetration test from an independent, third-party agency, and we are GDPR, HIPAA, ISO27001, and SOC2 Type 2 compliant as well as Data Privacy Framework certified.
Learn more




"Sentry's high-quality tooling helps Disney+ maintain high-quality service to its tens of millions of global subscribers."

Cool Vendors in Software Engineering: Improving Digital Resilience, January 2023. The GARTNER COOL VENDOR badge is a trademark and service mark of Gartner, Inc., and/or its affiliates, and is used herein with permission. All rights reserved. Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner's Research & Advisory organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.